Guard Your Logins, Own Your Future
Build Unbreakable Foundations
From Short Codes to Memorable Phrases
Length is leverage. Replace brittle eight-character puzzles with human-friendly passphrases built from unrelated words, occasional separators, and a dash of whimsy. Think diceware-like selections, gentle capitalization, and rare symbols, not birthdays or pet names. Sixteen characters or more resists brute force while remaining typable. Test readability aloud, then record only inside a password manager. When a site caps length, still choose the longest allowed. Comfort matters, but uniqueness and length matter more.
The Reuse Trap: One Leak, Many Doors
Attackers love credential stuffing because reused passwords let one breach unlock dozens of accounts. A leaked shopping login can become a stolen inbox, and then a cascade of password resets follows silently. Break the chain by using a unique, random secret per service. Let your manager generate everything. If something leaks, rotate only the affected account and anything federated through it. Reuse saves seconds today but can cost months of cleanup and worry.
Entropy Without Headaches: Practical Patterns
You do not need to memorize hundreds of random strings. Memorize exactly one strong passphrase for your password manager, secured with multi-factor authentication, and let it remember the rest. For memorable phrases, combine unrelated images, verbs, and places. Avoid predictable substitutions like 0 for o. Sprinkle structure sparingly so it remains unique. When unsure, prioritize manager-generated randomness. This approach delivers genuine entropy while keeping your mind clear for actual life and work.

Choosing a Trusted Vault

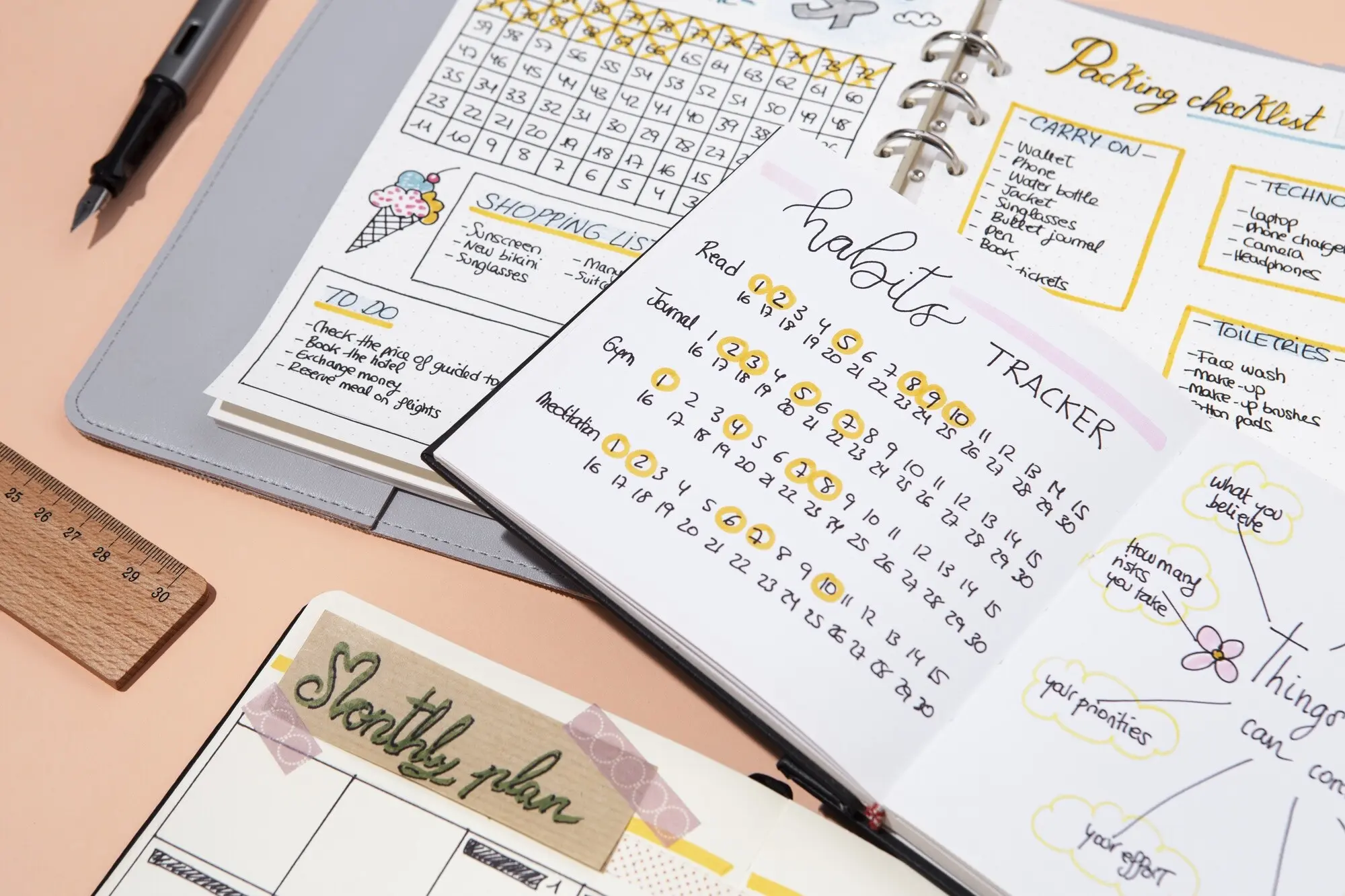
Daily Routines That Stick

An Afternoon Saved by Good Prep
Turn Second Factors into First-Class Protection

From SMS to Passkeys: An Upgrade Path
SMS beats nothing, but it is vulnerable to SIM swap and interception. Prefer TOTP from an authenticator app, then aim for FIDO2 or passkeys, which resist phishing by binding authentication to the real website. Start with email, bank, and password manager. Add cloud storage, domain registrar, and social accounts next. Keep printed recovery codes sealed securely. Document which services support passkeys and schedule upgrades monthly. Progress over perfection ensures meaningful gains without overwhelm.

Hardware Keys in Real Life
Carry two keys: one primary, one backup stored safely. Enroll both with each service and label them clearly. Practice a mock “lost key” drill so you know recovery steps before panic sets in. Consider a travel key on a simple keyring, leaving the backup at home. For shared admin duties, maintain a small, auditable pool. Hardware keys seem fussy until one day they quietly block a perfect-looking phishing page and prevent a crisis.
Defeating Push Fatigue and Phishing
Attackers bombard users with push requests, hoping for a tired tap. Enable number matching, location details, or require opening the authenticator to confirm. Favor passkeys or hardware keys that cannot be tricked by lookalike sites. Train yourself to reject surprises and verify initiator actions. If something feels off, cancel, change the password, and review sessions. Clear prompts, limited approvals, and strong factors together dismantle social engineering that thrives on urgency and distraction.
Mapping Your Accounts
Recovery That Actually Works

Small Habits, Big Shields
When Things Go Sideways, Bounce Back Fast
All Rights Reserved.